CLARITY’s Real Target: The Control Layer (Defaults, Holds, Routing)
Description current as of March 2026.
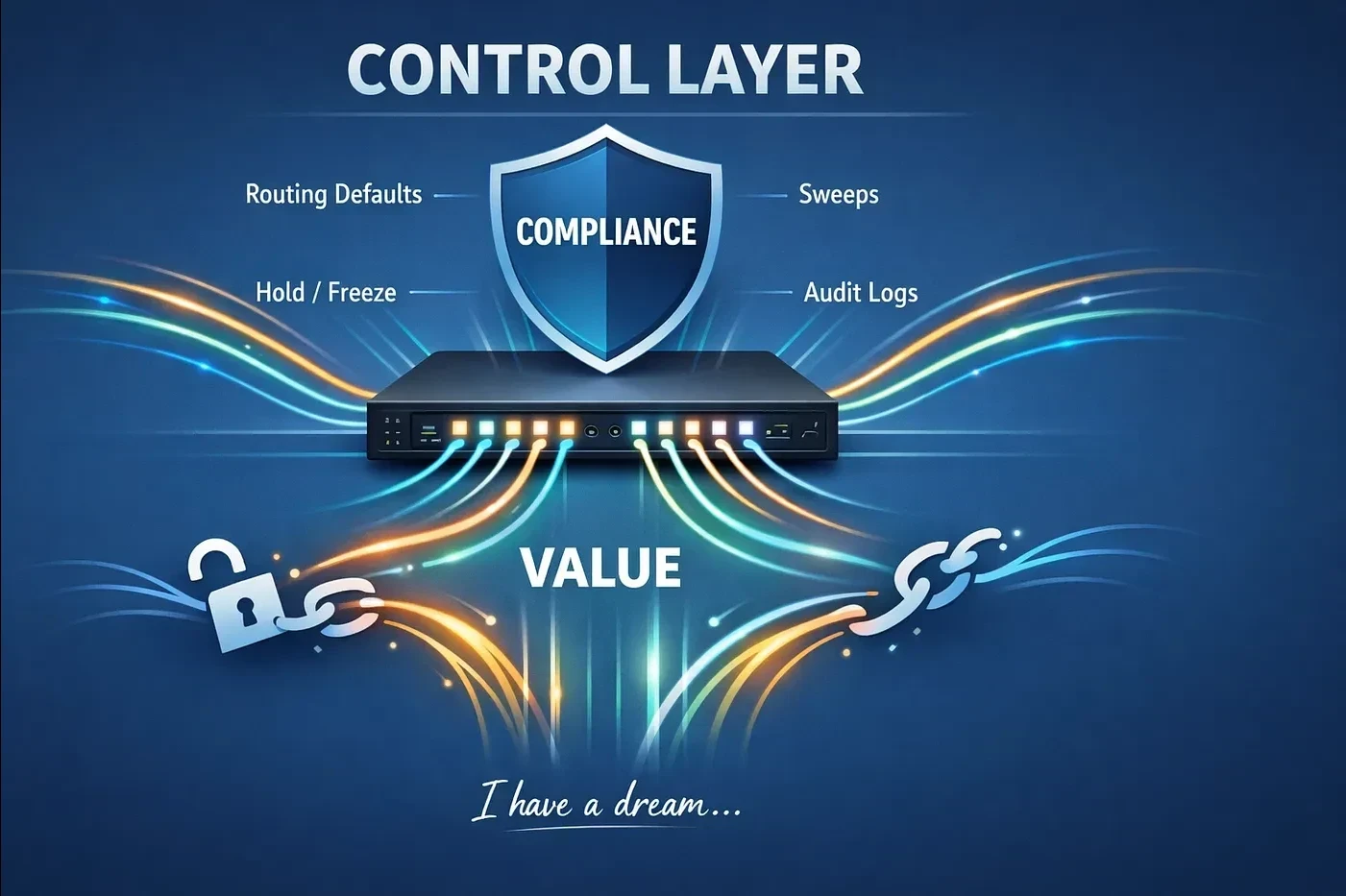
Most CLARITY debate is framed as a taxonomy fight: security versus commodity, SEC versus CFTC, “DeFi” versus “CeFi.” The essay argues that this is the wrong center of gravity. If CLARITY is implemented in anything close to its House-passed form, outcomes will be decided by where compliance gets encoded and who becomes the compelled operator of that compliance. In practice, the bottlenecks concentrate at the control layer: the interfaces people use, the routing defaults that determine where flow goes, the sweep engines that decide what balances become, and the hold/freeze plumbing that turns policy intent into executable, auditable operations.
Compliance attaches where it becomes operational. The essay reads the House-passed CLARITY text through a control-layer stack: anti-fraud authority over permitted payment stablecoins and certain digital commodity transactions; alternative trading system and venue operations; modernization of recordkeeping; and registration, custody, and customer-protection requirements for digital commodity intermediaries. The point is functional rather than formal: the practical bottlenecks are the front ends people use, the routing defaults that determine where flow goes, the sweep engines that decide what balances become, and the hold/freeze plus logging systems that make policy executable and auditable.
Three enforcement equilibria will compete. Issuer-centric (issuers and custodians carry most compliance load; interfaces stay light), router-centric (interfaces, defaults, and holds become the enforceable surface; regulated routers emerge), and infrastructure-gated (custody, venues, and market infrastructure define the acceptance standard). CLARITY’s text matters, but implementation chooses the equilibrium.
The framework is measurable. The essay defines operating metrics that turn design choices into governance problems: time-to-release (median and 95th percentile from hold to resolution), false-positive rate and appeal win rate, appeal throughput (cases per day per reviewer, backlog age), share of flows via compliant defaults, audit-log completeness (coverage, retention, tamper evidence), hold-duration distributions, case-documentation quality, repeat-offender patterns, and override governance.
What this piece changes
Most CLARITY analysis debates what tokens should be called. This piece shifts the question to who must do what when compliance becomes operational. The central insight is that the actor who owns the compliance primitive (the screening system, the routing engine, the hold workflow, the audit log) becomes the chokepoint, and that chokepoint determines where value capture and liability concentrate.
Core arguments
1. The operator rule: value follows the compliance primitive
When a compliance artifact becomes mandatory, the actor that owns it becomes the chokepoint. The compelled operator is typically the interface, router, or default owner. Required artifacts: screening, policy routing, audit logs, and hold workflows. The failure modes run in both directions: over-blocking produces false positives, complaints, churn, and political blowback; under-blocking produces enforcement, sanctions exposure, and reputational damage.
2. Two mechanics that decide market structure
Holds turn compliance into workflow. If holds and freezes become standard plumbing, the advantage goes to whoever owns the operational machinery: reversible state transitions, case management and reviewer tooling, notices, evidence packs, and exception handling. Weak operators lose on operations (slow error resolution, weak audit logs, brittle escalations), not on ideology.
Routing defaults become the product surface. In regimes that constrain token-level yield, defaults become the product: stablecoin balances swept into cash wrappers, payments routed through preferred rails, rewards implemented at the interface through “activity” rules, compliance implemented through routing, logs, and holds. Defaults shape flow; flow determines rents.
3. Three fault lines that flip the switch
Rewards: where yield is allowed to live. If token-level interest is constrained, yield migrates to wrappers, sweeps, and default allocators. Whoever controls that allocation layer captures the economics.
App-layer scope: control-based versus code-based perimeter. The core DeFi question: do obligations attach to who can route and modify outcomes, or to who wrote the software? The essay argues that “routing control” is becoming the practical test. Entities that can run compliance at scale convert it into distribution advantage.
Tokenization: loophole narratives versus plumbing reality. Institutions scale tokenization when liability is legible, records reconcile, and finality is defensible. The infrastructure that can produce repeatable, auditable equivalence evidence captures value. This connects directly to the MVEP framework.
4. “Truth-in-equivalence” is the price of institutional scale
Every serious tokenized product needs an equivalence pack: rights mapping (legal and economic equivalence), records and reconciliation (how ledgers match, how breaks are resolved), custody and segregation (including insolvency posture), finality and exception handling (reorgs, reversals, dispute resolution), and governance and audit logs (who can change what; how it is proven after the fact). Without documented equivalence, a product is a pilot, not an institutional offering.
Two decision overlays
For Congressional staff: five questions that determine outcomes
- What counts as activity-based rewards versus indirect inducement?
- Is app-layer scope defined by control or by code?
- What is the due-process floor for holds (notice, appeal, time limits)?
- Does offshore reporting become gateway gating via guidance?
- Is this one perimeter, or a federal-plus-50-state stack?
For bank directors: what you must decide
- Where deposit beta moves (defaults, sweeps, wrappers)
- Where compliance cost concentrates (front doors, hold operations)
- Where tail risk sits (who absorbs sanctions and fraud errors)
- Whether you sponsor issuance, custody, routers/wrappers, or accept commoditization
What problem it solves
CLARITY will be positioned as clarity about what things are. It will function as clarity about who must do what, and who becomes responsible when something goes wrong. Token labels matter; routers, defaults, and holds decide outcomes. This piece maps where compliance becomes code, liability becomes workflow, and value capture shifts toward regulated routers and infrastructure gatekeepers.
Anchor evidence / policy inputs
This is a control-layer policy essay. It is anchored on:
- CLARITY Act, in the House-passed form analyzed here, including anti-fraud, venue, recordkeeping, intermediary-registration, custody, and customer-protection provisions that can push compliance toward interfaces, defaults, logs, and hold workflows.
- GENIUS Act (enacted), which defines the payment-stablecoin perimeter that market-structure rules under the CLARITY Act (House-passed form analyzed here) would sit on top of.
- Dollar v3 as the companion essay, which provides the three-object, Layer 0, and deposit-effects framework this piece operationalizes.
- MVEP, which supplies the institutional “truth-in-equivalence” standard referenced in the institutional-scale section.
The three enforcement equilibria and operating metrics are the author’s analytical framework. They describe where compliance could concentrate under the House-passed text analyzed here, conditional on implementation choices and later revisions.
Limitations
- This is a policy essay expressing the author’s analytical framework; it is not legal advice or a section-by-section statutory memo.
- The operative text analyzed here is the House-passed CLARITY form; later Senate or conference revisions could materially change the mapping.
- The three enforcement equilibria are scenarios for where compliance could concentrate; implementation will determine which dominates.
- Operating metrics (time-to-release, false-positive rate, audit-log completeness, etc.) are proposed monitoring standards, not observed measurements from live systems.
Want to discuss this paper? [email protected]